Parent class: TrojWare
Trojans are malicious programs that perform actions which are not authorized by the user: they delete, block, modify or copy data, and they disrupt the performance of computers or computer networks. Unlike viruses and worms, the threats that fall into this category are unable to make copies of themselves or self-replicate. Trojans are classified according to the type of action they perform on an infected computer.Class: Trojan
A malicious program designed to electronically spy on the user’s activities (intercept keyboard input, take screenshots, capture a list of active applications, etc.). The collected information is sent to the cybercriminal by various means, including email, FTP, and HTTP (by sending data in a request).Read more
Platform: Win32
Win32 is an API on Windows NT-based operating systems (Windows XP, Windows 7, etc.) that supports execution of 32-bit applications. One of the most widespread programming platforms in the world.Description
Technical Details
This Trojan is designed to steal user passwords. It is a Windows PE EXE file. It is 57,821 bytes in size. It is packed using UPX. The unpacked file is approximately 73KB in size.
Installation
When launching, the Trojan extracts the following files from its body:
- %System%Bk_client.htm – 9,370 bytes in size;
- %System%CONNECT.htm – 7,468 bytes in size;
- %System%ATOMIC.GIF – 10,240 bytes in size.
Once the Trojan has extracted %System%Bk_client.htm from its body, the Trojan itself will be launched.
The Trojan also adds the following parameter to the system registry:
"Bk_client.htm" = "%System%Bk_client.htm"
This ensures that each time the operating system is loaded, Internet Explorer will be launched, opening %System%Bk_client.htm.
Payload
This program is designed to hack a Russian game called 'Boitsovskii klub’ (Fight Club). However, this is a fake program, and the Trojan will actually conduct the following actions:
When launched, the Trojan displays the following window:
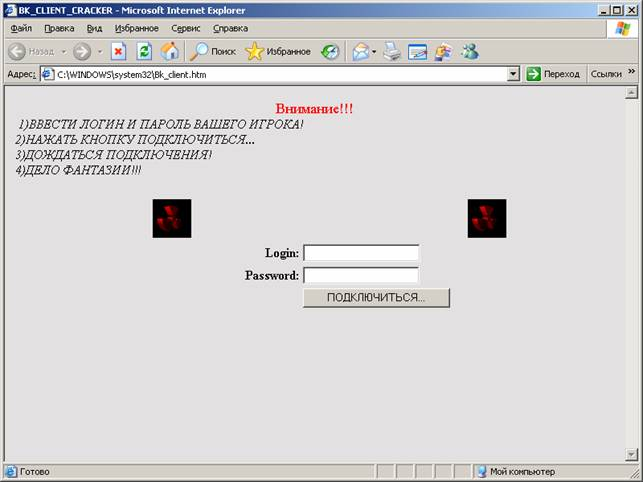
When the user clicks on the button ‘Podkluchit’sya’ (‘Connect’) the Trojan will send the data entered in the ‘Login’ and ‘Password’ fields by email to the remote malicious user at ****et777@rambler.ru. The Trojan uses the following script to send email:
http://world-market.com/cgi-bin/mailto.pl
Once the email has been sent, the browser loads a page from %System%CONNECT.htm in a pop-up window:
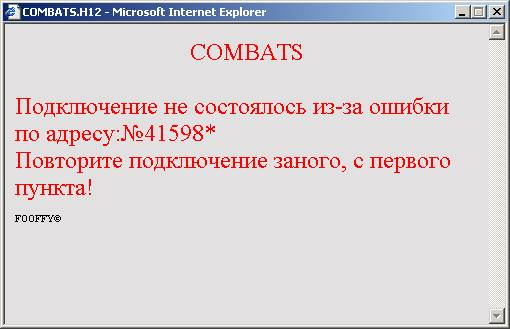
This window informs the user that the connection was unsuccessful, and instructs the user to repeat the connection process from step one.
Removal instructions
If your computer does not have an up-to-date antivirus, or does not have an antivirus solution at all, follow the instructions below to delete the malicious program:
- Delete the following files:
%System%Bk_client.htm %System%CONNECT.htm %System%ATOMIC.GIF
- Delete the following system registry key parameter:
[HKLMSOFTWAREMicrosoftWindowsCurrentVersionRun]
"Bk_client.htm" = "%System%Bk_client.htm" - Update your antivirus databases and perform a full scan of the computer (download a trial version of Kaspersky Anti-Virus).
Read more
Find out the statistics of the vulnerabilities spreading in your region on statistics.securelist.com
Found an inaccuracy in the description of this vulnerability? Let us know!