Parent class: TrojWare
Trojans are malicious programs that perform actions which are not authorized by the user: they delete, block, modify or copy data, and they disrupt the performance of computers or computer networks. Unlike viruses and worms, the threats that fall into this category are unable to make copies of themselves or self-replicate. Trojans are classified according to the type of action they perform on an infected computer.Class: Trojan
A malicious program designed to electronically spy on the user’s activities (intercept keyboard input, take screenshots, capture a list of active applications, etc.). The collected information is sent to the cybercriminal by various means, including email, FTP, and HTTP (by sending data in a request).Read more
Platform: Win32
Win32 is an API on Windows NT-based operating systems (Windows XP, Windows 7, etc.) that supports execution of 32-bit applications. One of the most widespread programming platforms in the world.Description
Technical Details
This Trojan is written in Assembler, and is not packed in any way. The file is 8,192 bytes in size.
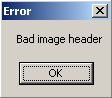
If the Trojan is launched from a directory other than %Windir%, the following error message will be displayed:
Once launched, the Trojan copies itself to the Windows system directory as "pic.exe":
%Windir%pic.exe
It then adds the string pic.exe to the load key in win.in:
load=pic.exe
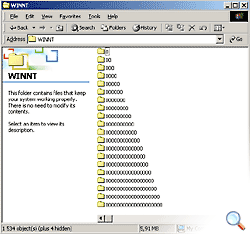
The Trojan then creates 1500 folders in the Windows directory with names composed of zeros, ones, twos, threes, fours and fives.
The Trojan contains the following strings:
Macur-Copyright 1998-1999. 17 Apr 1999, ***im@duck.odessa.ua, ICQ# **216706
Removal instructions
- Delete the original Trojan file (the location will depend on how the program originally penetrated the victim machine).
- Delete the file created by the Trojan:
%Windir%pic.exe
- Delete the following string from win.ini (only for Windows 95/98/Me):
load=pic.exe
- Delete all folders created by the Trojan.
- Update your antivirus databases and perform a full scan of the computer (download a trial version of Kaspersky Anti-Virus).
Read more
Find out the statistics of the vulnerabilities spreading in your region on statistics.securelist.com
Found an inaccuracy in the description of this vulnerability? Let us know!