Parent class: TrojWare
Trojans are malicious programs that perform actions which are not authorized by the user: they delete, block, modify or copy data, and they disrupt the performance of computers or computer networks. Unlike viruses and worms, the threats that fall into this category are unable to make copies of themselves or self-replicate. Trojans are classified according to the type of action they perform on an infected computer.Class: Trojan-PSW
Trojan-PSW programs are designed to steal user account information such as logins and passwords from infected computers. PSW is an acronym of Password Stealing Ware. When launched, a PSW Trojan searches system files which store a range of confidential data or the registry. If such data is found, the Trojan sends it to its “master.” Email, FTP, the web (including data in a request), or other methods may be used to transit the stolen data. Some such Trojans also steal registration information for certain software programs.Read more
Platform: Win32
Win32 is an API on Windows NT-based operating systems (Windows XP, Windows 7, etc.) that supports execution of 32-bit applications. One of the most widespread programming platforms in the world.Description
Technical Details
This program belongs to the family of passwords stealing trojans. It was spread from a public access Web page on the narod.ru server in the beginning on June 2002.
The web page contained the following:
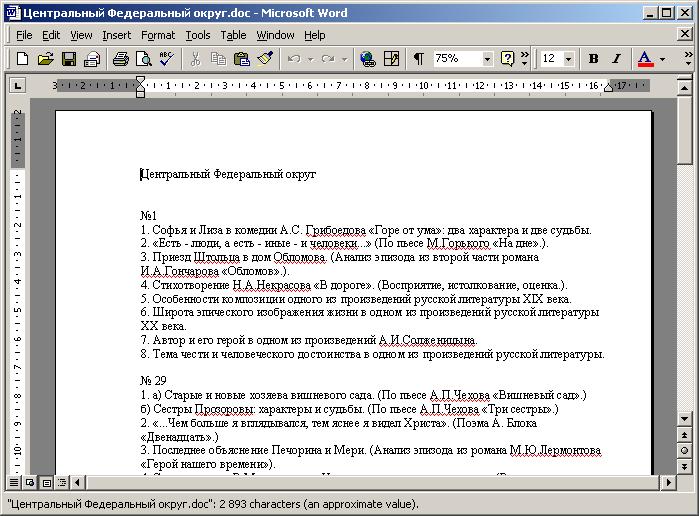
Intermediate Examinations Test papers for mathematics and topics for compositions. Still FREE!
The file residing on the web page is a Trojan installer. When run it drops a Trojan program into the Windows directory, then extracts and createes fake examination topics (in Russian).
The Trojan itself is a Windows PE EXE file about 27Kb in length (compressed by UPX, the decompressed size is about 83Kb) and written in Delphi.
When executed the Trojan copies itself to the Windows directory under the SYSTEM.EX name and registers this file in system registry auto-run key:
HKLMSoftwareMicrosoftWindowsCurrentVersionRun System = %WindowsDir%System.exe
The main function for the CrazyBilets Trojan are collecting cached Windows passwords on victim machines and sending this information to its "master" by direct connection to an SMTP server.
Read more
Find out the statistics of the vulnerabilities spreading in your region on statistics.securelist.com