Parent class: TrojWare
Trojans are malicious programs that perform actions which are not authorized by the user: they delete, block, modify or copy data, and they disrupt the performance of computers or computer networks. Unlike viruses and worms, the threats that fall into this category are unable to make copies of themselves or self-replicate. Trojans are classified according to the type of action they perform on an infected computer.Class: Trojan
A malicious program designed to electronically spy on the user’s activities (intercept keyboard input, take screenshots, capture a list of active applications, etc.). The collected information is sent to the cybercriminal by various means, including email, FTP, and HTTP (by sending data in a request).Read more
Platform: Win32
Win32 is an API on Windows NT-based operating systems (Windows XP, Windows 7, etc.) that supports execution of 32-bit applications. One of the most widespread programming platforms in the world.Description
Technical Details
This Trojan is a Windows PE EXE file. It is approximately 245KB in size (the file size may vary slightly). It is written in Borland Delphi.
Payload
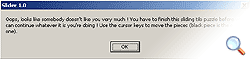
Once launched, the Trojan will cause a message to be displayed information the user that s/he has to assemble the puzzle composed of squares on the screen by moving the pieces using the cursor keys:
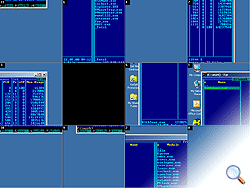
Once the user clicks on OK, the Trojan splits the Windows desktop into 11 square pieces, and jumbles them up:
Once this has been done, it will be impossible to use any Windows applications.
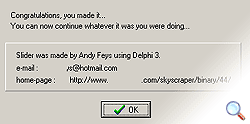
The user can move the pieces using the arrow keys. Once the user has placed the pieces in the correct order, a message containing information about the Trojan and its author will be displayed:
Removal instructions
- Terminate the Trojan activity by pressing Alt+F4.
- Delete the original Trojan file (the location will depend on how the program originally penetrated the victim machine).
- Update your antivirus databases and perform a full scan of the computer (download a trial version of Kaspersky Anti-Virus).
Read more
Find out the statistics of the vulnerabilities spreading in your region on statistics.securelist.com