Parent class: TrojWare
Trojans are malicious programs that perform actions which are not authorized by the user: they delete, block, modify or copy data, and they disrupt the performance of computers or computer networks. Unlike viruses and worms, the threats that fall into this category are unable to make copies of themselves or self-replicate. Trojans are classified according to the type of action they perform on an infected computer.Class: Trojan-Spy
Trojan-Spy programs are used to spy on a user’s actions (to track data entered by keyboard, make screen shots, retrieve a list of running applications, etc.) The harvested information is then transmitted to the malicious user controlling the Trojan. Email, FTP, the web (including data in a request) and other methods can be used to transmit the data.Read more
Platform: HTML
Hypertext Markup Language (HTML) is the standard markup language for documents interpreted by web browsers. Markup of most web pages and web applications is written in HTML or XHTML.Description
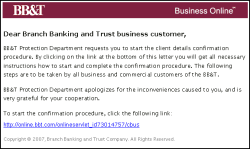
This Trojan uses spoofing technology. It is a fake HTML page. It is designed to steal confidential information from BB&T clients. This Trojan was originally mass mailed.
The Trojan arrives in the guise of an important email from BB&T:
The email contains a link which exploits the Frame Spoof vulnerability in Internet Explorer.
If the user clicks on the link, visits the site, and enters his/ her account details, they will be sent to the remote malicious user, who may then have full management rights to the user's profile.
The Frame Spoof vulnerability (MSO4-004) is present in Microsoft Internet Explorer 5.x and 6.x. Microsoft published a describing the vulnerability and how to recognize such fake links.
Read more
Find out the statistics of the vulnerabilities spreading in your region on statistics.securelist.com